In our first article, we looked into what the Cyber Resilience Act (CRA) means for industrial device makers and machine builders who develop or brand their own connectivity.
This second article steps back from the “what” and instead answers a different question: Why is the CRA being introduced at all, and why is it necessary, despite the disruption it creates?
To understand this, we need to look at why voluntary security hasn’t worked, what CRA gets right, how device makers and machine builders ultimately benefit, and what CRA will not magically fix.
For decades, industrial automation has relied on voluntary security practices. Many manufacturers have done their best with the resources available, but voluntary security has struggled for four key reasons.
Industrial equipment is remarkably diverse. Devices come from different generations, run different operating systems, and interact with a mix of legacy networks, cloud interfaces, and proprietary protocols.
In such a fragmented environment, consistent voluntary security was impossible. Every manufacturer did security “their own way,” with varying levels of maturity.
A typical industrial device remains in service for 10 to 20 years.
Voluntary security breaks down over such long-time spans. Software libraries change, suppliers disappear, developers move on, and no one is formally responsible for patching something built a decade ago.
Security simply could not keep pace with lifecycle realities.
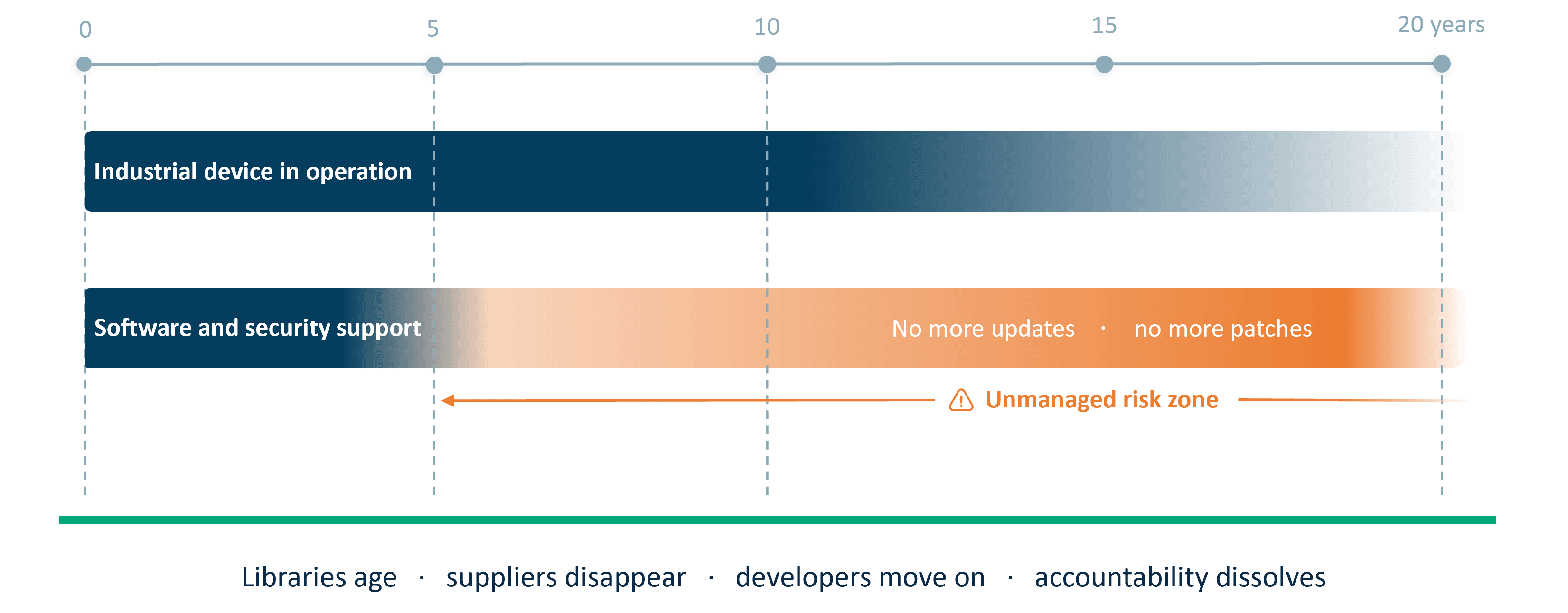
Figure 1. Long product lifecycles create a security gap
In industrial environments, productivity has traditionally been the dominant priority. Changes to improve security creates downtime, which directly affects production, revenues, and customer commitments.
As a result, security was often treated as a secondary concern and addressed only if it did not interfere with performance, determinism, or operational stability. Security updates were postponed to avoid production downtime, and architectural changes were avoided to not disrupt stability
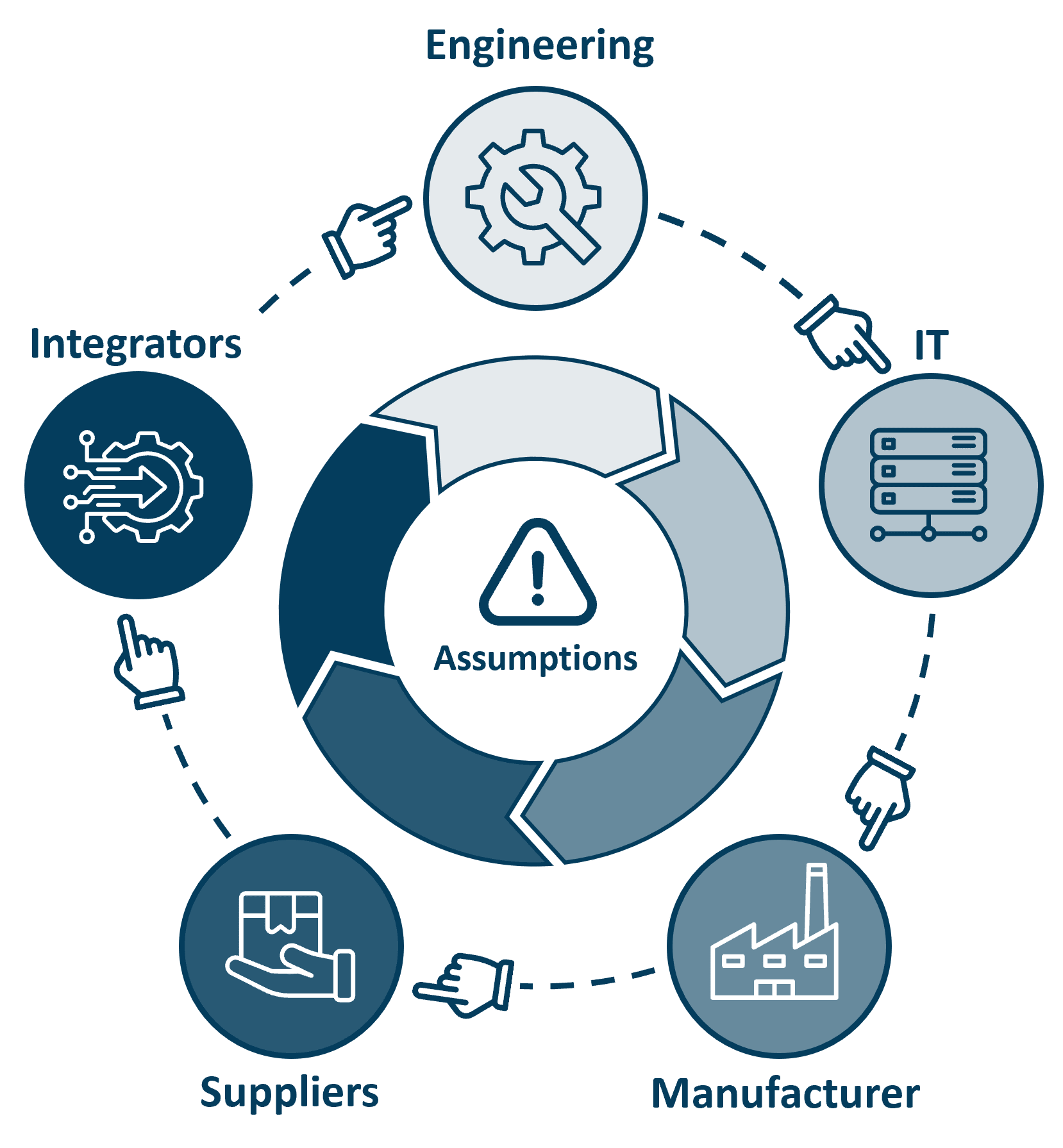
Perhaps the most important point:
Everyone assumed someone else was responsible.
There is also a deeper economic reason why voluntary security has struggled: the impact of a cyber incident often extends beyond the organization that made the cost decision.
The European Commission estimates the global annual cost of cybercrime at around €5.5 trillion, underlining the scale of the problem and why cybersecurity has become a societal concern, not just a company issue.¹
In practice, a device maker, machine builder, or facility owner might calculate that investing in cybersecurity is not justified by the direct financial risk they personally carry. But the real impact of a cyber incident can often fall elsewhere, on customers, citizens, and society.
This is one reason the EU sees a need to regulate: without clear requirements, normal market forces do not always drive sufficient investment in cybersecurity, a concern explicitly addressed in the EU’s cybersecurity strategy.². It can even become a “chicken and egg” problem. If customers do not demand cybersecure products, manufacturers have little incentive to supply them. And if secure products are not widely available, demand stays low.
The EU cybersecurity strategy addresses this split directly: NIS2 focuses on cybersecurity responsibilities for operators and facility owners, while the Cyber Resilience Act (CRA) sets mandatory requirements for device makers and machine builders placing products with digital elements on the market.
Real world incidents show why this regulatory approach is necessary. Cyber incidents can disrupt critical production and services, and the consequences can reach far beyond the company that was attacked ³,⁴,⁵,⁶,⁷.
In short, the voluntary model didn’t work. CRA emerged because the industry needed a more reliable, accountable foundation for connected products.
Despite the disruption it brings, the CRA addresses the root causes of this long-standing security inconsistency. And it gets several important things very right.
CRA places responsibility squarely on the manufacturer of the product with digital elements.
For device makers and machine builders, this means:
This aligns responsibility with control, a major improvement.
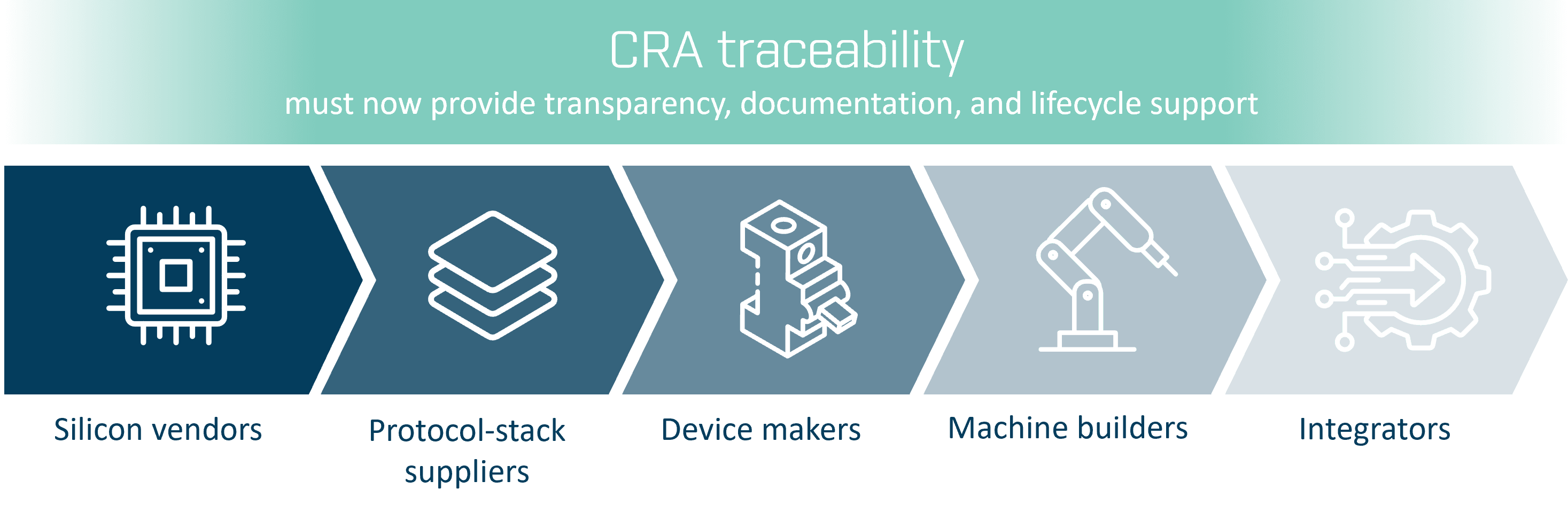
Under CRA, every participant - silicon vendors, protocol stack suppliers, device makers, machine builders, integrators - must now provide transparency, documentation, and lifecycle support.
CRA replaces assumptions with traceability.
In the past, security could be “added later” or addressed only when needed. CRA changes the engineering mindset:
Security becomes part of the product from day one, not an afterthought.
Before looking at the specific advantages, it is worth asking a broader question:
What long term benefits will the CRA create for device makers and machine builders?
While CRA brings short term disruption, many long term benefits quickly become clear.
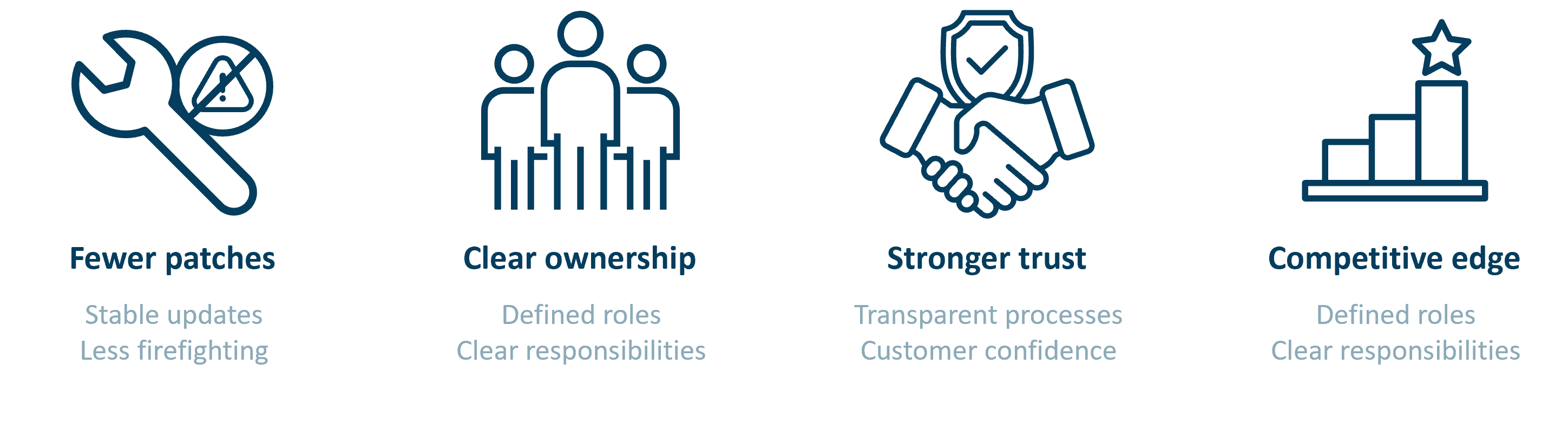
Structured vulnerability handling and secure update mechanisms drastically reduce “Friday night emergency fixes” and firefighting.
Before CRA, security responsibilities were scattered: engineering had some, IT had some, product management had some. CRA forces companies to define roles and responsibilities clearly.
This reduces confusion and strengthens internal alignment.
End customers or system integrators increasingly demand security assurances.
With CRA, device makers and machine builders can provide:
• documented processes
• traceable updates
• structured security evidence
This builds trust, and trust increasingly influences purchasing decisions.
As large industrial players begin demanding CRA readiness in their requests for quotations (RFQs), compliant device makers and machine builders gain a clear advantage.
CRA becomes a differentiator, not only a requirement.
To stay realistic, it’s important to understand what CRA does not change.
Security-by-design requires time, resources, testing, documentation, and new processes.
The workload doesn’t vanish, it becomes more structured.
No regulation can prevent cyberattacks.
What CRA does is ensure devices are designed to withstand them with the right level of resilience and transparency.
CRA requires real expertise. Templates, checklists, and conformity assessments cannot replace experienced security engineering.
CRA is a framework, not a shortcut.
CRA adds new expectations, new processes, and long term responsibilities - and it forces difficult changes.
But it also fixes structural weaknesses that have made industrial cybersecurity inconsistent for years.
For industrial device makers and machine builders, CRA is not just another regulation. It is an opportunity to strengthen product security, build customer trust, and align with modern expectations for connected equipment.
In the next article, we will examine why legacy connectivity is difficult to make CRA compliant and how replacing it with a modern CRA ready connectivity solution simplifies compliance.
Whether you are updating existing devices or designing new ones, the right connectivity strategy is key to CRA readiness. Learn more about the Cyber Resilience Act and explore Anybus gateway and embedded solutions that help you build secure, maintainable, and future-ready devices.
Dr. Jens Jakobsen
Product Security Manager, HMS Networks
Dr . Jens Jakobsen is Product Security Manager at HMS Networks, where he leads the company’s work to strengthen the cybersecurity of industrial communication products and protect connected equipment from emerging threats. He brings extensive experience from technical and leadership roles at HMS Networks, Schneider Electric, and Motorola Solutions, and has worked for many years with industrial communications and cybersecurity. Dr. Jakobsen holds seven granted patents in telecom and industrial communication technologies.
References
1. European Commission – Cyber Resilience Act background and impact https://digital-strategy.ec.europa.eu/en/library/cyber-resilience-act
2. European Commission – EU Cybersecurity Strategy https://digital-strategy.ec.europa.eu/en/policies/cybersecurity-strategy
3. MedTech Dive – Stryker’s manufacturing and shipping disrupted after cyberattack https://www.medtechdive.com/news/strykers-manufacturing-shipping-disrupted-after-cyberattack/814667/
4. SVT Nyheter – Sensitive personal data published after Sportadmin cyberattack https://www.svt.se/nyheter/inrikes/kansliga-uppgifter-har-publicerats-efter-attacken-mot-sportadmin
5. Ingeniøren – Cyberattack on water utility caused physical disruption to water supply https://ing.dk/artikel/pro-russisk-cyberangreb-efterlod-borgere-uden-vand-i-flere-timer
6. FireEye – TRITON / TRISIS attack on industrial safety systems https://www.fireeye.com/blog/threat-research/2017/12/attackers-deploy-new-ics-attack-framework-triton.html
7. BBC – German steel mill cyberattack causes massive damage https://www.bbc.com/news/technology-30575104